
How to Defend Against Smishing Attacks
Healthcare data has significant value for hackers, and older adult care is one of the most targeted industries. Hackers use personal data to access patient healthcare information, create false identities, commit insurance fraud or obtain free medical treatment.
Knowing how to prevent smishing attacks is crucial to protect patients and your bottom line. A healthcare data breach can have devastating consequences. It can cause care disruptions, jeopardize patient privacy and eliminate an entire healthcare network. Recovery from a cyberattack can cost millions of dollars, and attacks on the healthcare industry are increasing. In a recent survey, 21% of healthcare organizations claimed they had been victims of a smishing attack.
What Is a Smishing Attack?
Let’s take a look at the meaning and definition of smashing. Smishing is a type of short message system (SMS) phishing — the name is a combination of “SMS” and “phishing.” These cyberattacks use social engineering to exploit human trust. Hackers send fraudulent messages to trick recipients into clicking on a malicious link or sharing personal information. People tend to trust text messages more than emails, which has led to a 300% increase in smishing scams within two years.
How Does Smishing Work?
Smishing is almost identical to email phishing, where the attacker wins your trust through manipulation. Cybercriminals send you a message via SMS or instant message, enticing you to click a link or reply with your personal information.
If you click the link in a smishing message, the cybercriminals have two ways to steal the data they want:
- The link may direct you to a fraudulent version of an official website, directing you to fill out a form containing your personal information.
- Clicking the link may download malware onto your device, allowing them to access your sensitive information.
Since healthcare providers must keep patient data safe, hackers may also use phishing and smishing to install ransomware.
How Does Smishing Spread?
Scammers can deliver smishing messages through traditional messaging and web-based messaging applications. Users often assume that text messages are more trustworthy than emails. Many people also multitask on their phones, making them more likely to click links in a hurry or by mistake.
Many healthcare workers use their devices in the scope of their work. While this bring-your-own-device (BYOD) has enhanced efficiency and productivity, it has significant cybersecurity challenges. Smishing uses malware to spread throughout networks. Once cyberattackers breach one network-connected device, they can access the entire network, gaining access to sensitive patient data.
Types of Smishing Attacks
Smishing is a phishing method and hackers can deliver many types of phishing scams via text message, including the following:
- Spear phishing: In this more direct attack, hackers target a specific team or individual within your organization instead of sending generic messages.
- Whaling: Whaling attacks either target or impersonate high-value individuals within the organization. Impersonating a senior executive is an excellent method of convincing employees to make payments or divulge sensitive information.
- Clone phishing: Attackers may clone legitimate text messages instead of impersonating someone else. They alter the link slightly, taking you to a cloned replica of the original site where you’ll feel comfortable providing your personal information.
- Vishing: A vishing scam is similar to smishing, except scammers use voice calls instead of text and email. Vishing and smishing sometimes go hand in hand as a social engineering technique.
- IM smishing: This attack targets users through instant messaging, such as Facebook messenger. It may come from a stranger or what appears to be one of your contacts. Hackers sometimes create spoofed accounts, pretending to be someone you know to gain your trust.
How to Recognize Smishing
Recognizing a smishing text message is the first step to preventing smashing attacks. Look for the following signs to help you identify them:
- Text messages that ask for personal information or entice you to click on a link
- A sender name or number that resembles a legitimate entity but has one or two different characters
- Spelling and grammatical errors
- Unexpected messages or messages from senders you haven’t spoken to before
- Text messages with a sense or urgency or threat of immediate action

How to Defend Against Smishing
Defending against smishing attacks is critical for patient care, data safety and profitability. The HIPAA privacy rule requires covered healthcare organizations to implement a security awareness training program to protect sensitive patient data. While vital, these training sessions are only a starting point. As cybercriminals become more adept, specialist IT services are a must for many.
Complementary methods of smishing defense include the following:
1. Employee Training
Smishing targets individuals, so staff must be able to recognize smishing attempts and know the protocols for reporting them. Training might include running mock smishing events to identify potential weaknesses in your team. As smishing scams evolve, healthcare organizations should provide ongoing training as needed. Regular training will help healthcare professionals recognize and report new trends.
2. Cybersecurity Measures
Protecting yourself and your organization from smishing attempts requires IT professionals with considerable expertise. A trained team will identify and patch network weaknesses, implement endpoint security systems and keep antivirus software up to date. They will conduct regular vulnerability scans across your network and block malicious domains as they are identified.
Many smashing scams use spoofing technologies to mimic a legitimate website, manipulating users into filling in their personal details. As many healthcare providers rely on their mobile devices for their work, implementing anti-spoofing technologies to minimize fraudulent websites can be crucial.
3. Communication
Healthcare organizations must stay current with the latest scams and communicate the dangers throughout their organization to defend their data. If vulnerable parties know what to look for, they are less likely to fall prey to smashing attempts.
Examples of Smishing
Cyberattacks are constantly evolving as cybercriminals engineer their attempts to catch you off guard. For example, the New Hampshire COVID-19 smishing campaign claimed to provide test results and asked recipients to validate their COVID-19 status.
Some common smishing examples include the following:
- Competition wins: Receiving a message informing you that you’ve won a contest is a well-known red flag. Clicking on the link to claim your prize can cause you to accidentally install malware on your device instead.
- Surveys: Smishing attempts can take the form of surveys, often claiming you’ll win a prize if you answer the questions. If they ask you to click on a link, there’s a strong possibility it’s a smishing attempt.
- Delivery notifications: Scammers know there’s a good chance you’re waiting for a delivery. Even if you’re not, you may click on a link that looks like it comes from a trusted brand. Many delivery companies offer legitimate updates, making this an easy entry point for scammers to confuse you.
- CEO fraud: Hackers sometimes rely on people’s instincts to reply to a boss’s request as soon as possible. They may send a message that looks like it comes from someone in your organization claiming to need immediate assistance with a task.
- Bank or credit card scams: Receiving a message about your money can be stressful and cybercriminals use this anxiety to get you to act quickly. These scams often ask you to verify your banking or contact information.
- Fake password resets: With many people using two-factor authentication to protect their data, scammers may send a text message claiming your account has experienced a breach. When this happens, they have already established your phone number and email address. They’ll send a code to reset your password and a link to a spoofed email site that asks you to enter your login information. Once they have your password, the hackers will either sell the information, take control of your account or use it to send more phishing emails.
- Cellphone smishing: Scammers may pose as your mobile service provider and offer you discounts or upgrades. These messages often include a link to activate the offer, taking you to a spoofed website that prompts you to confirm your personal information.
- Tax scams: Hackers often take advantage of tax season with messages claiming that you owe money or are due a refund. They install malware on your device when you click the link to make payments or retrieve your money.
While these attacks personally affect the victim, they also grant hackers access to their work networks and sensitive patient data. Malware travels rapidly through an organization’s network and can cause significant damage without effective and professional cybersecurity protection.
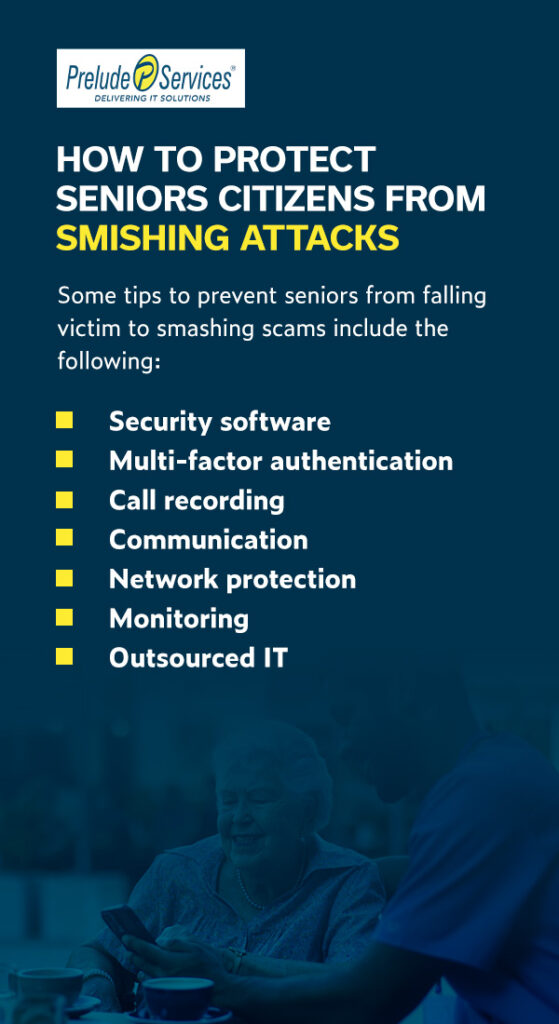
How to Protect Seniors Citizens from Smishing Attacks
Educating older adults is the most effective way to prevent smishing. Make them aware of common scams and ask them to verify any texts they receive with you or the sender via telephone.
The more you can do to stop scammers from making contact with older adults, the better. Loneliness, diminished cognitive reasoning and accrued savings often make them prime targets for scammers.
Some tips to prevent seniors from falling victim to smashing scams include the following:
- Security software: Ensure older adults have updated security software on their devices and check that it updates automatically.
- Multi-factor authentication: Familiarize older adults with multi-factor authentication for all social media and online accounts. Activate biometrics on their devices to prevent unwanted access.
- Call recording: Many smishing attempts begin with a phone call. They can install a call recording app on their devices to monitor suspicious conversations or requests.
- Communication: Stay abreast of the latest scams so you can advise the older adults in your care. Print posters and display them in common areas as a constant reminder.
- Network protection: Set up proxy servers with robust security for your internet connections and install anti-spam solutions.
- Monitoring: Monitor your security log for intrusions, suspicious activity and attacks. Conduct regular vulnerability scans of your network to assess your cyber risk.
- Outsourced IT: Outsourced IT services can help protect your network from a breach. They can also provide training and keep you up to date with the latest scams.
Teaching Older Adults to Steer Clear of Smishing Attempts
Teaching older adults how to approach text communication correctly is one of the most powerful methods of helping them avoid financial fraud and scams. Make them aware of the following cybersecurity practices for their personal devices:
- Avoid clicking on links: If links appear in a text message, only click on them if you initiated the original communication and are confident it comes from a trusted source.
- Type web addresses out: Instead of clicking on a link that takes you to a website, type the website directly into the browser.
- Check security certificates: You can check a website’s security status by clicking on the padlock icon in the left corner of the browser. The website should always begin with HTTPS, which means any information you share through the website remains private.
- Refuse to send personal information over text message: Teach older adults that there is no need to share personal information over text or phone.
- Call and confirm: If you receive a communication from a company, colleague or well-known brand, call and confirm the contact before acting on it.
- Reach out: Many older adults experience shame after falling victim to a phishing or smashing scam. Encourage them to speak up and provide a supportive environment where they can share their experiences.
What to Do if You’re a Victim of Smishing
It’s important to know what to do if you become a victim of smishing. Stay calm and take the following steps:
- Change your passwords: Once a hacker has access to your device, they have access to your passwords. Change them as quickly as possible, then log out of the device.
- Disconnect and call IT Support: As soon as you realize what’s happened, disconnect from all networks immediately to limit the spread of malware. Smishing can happen to anyone and your outsourced IT team is the best prepared to deal with it. Contact them and follow their instructions. They will let the rest of the organization know.
- Have your device scanned: If you clicked on a suspicious link, hackers might have downloaded malware onto your device. Ask an IT professional to scan your device for viruses and malware.
- Report the attack: There are several organizations you can report the attack to, including your local police station and the federal trade commission. Your IT support provider can guide and support you through the process.
- Stay alert: Be aware of future attempts to breach your device, as the hackers may try again. Report anything suspicious and verify any links before you click on them.
Contact Prelude Services for Complete IT Services
Healthcare organizations have massive amounts of data to manage and cybersecurity is one of many IT processes you need to consider. Prelude Services provides an inclusive IT service for your healthcare facility, including 24/7 desktop support, mobile device management and HIPAA IT risk assessment, ensuring your data are as safe as possible.
If you’re looking for a reliable, safe IT service you can trust, look no further than Prelude Services. We believe that IT services in healthcare should be accessible and reliable so you can care for patients without stress and downtime. Please reach out to us today to learn more about how we can streamline your IT processes, manage your network and keep your data safe.
CONTACT PRELUDE SERVICES FOR 24/7 IT SUPPORT
Technology has become a crucial part of the modern business experience. Without functional computers and mobile phones, many business practices would grind to a halt. Unfortunately, breakdowns and malfunctions are an inevitable part of any machine, meaning businesses do grind to a halt until the issues are fixed. In order to keep your business running, it's crucial to have access to IT support when you experience technical difficulties.
If you're a healthcare company, long-term care provider, or small business in need of IT support at all hours, consider Prelude Services. We're a SSAE SOC
Compliant business dedicated to improving your security and functionality. We offer specific IT services for senior living care, nursing homes, retirement home services and assisted living, including 24/7 IT support. If you want to know how Prelude can help you, contact us today!

