The Ultimate Guide to Phishing Attacks & How to Avoid Them
Phishing attacks are still around and are just as concerning as they’ve always been. In fact, phishing attacks have grown more sophisticated, targeting high-value victims as hackers attempt to trick users into divulging important information or downloading malware. Both businesses and individuals must take phishing seriously to avoid detrimental effects on data, finances and business assets.
Since phishing scams can be so intricate, you need to have a strong understanding of what they look like and what you can do to prevent them. To make it easier, we’ve put together a comprehensive guide to phishing scams. Let’s dive into the details of phishing, how to avoid phishing scams, and what to do if you’ve clicked on a phishing scam link.
What Is Phishing?
Phishing can come in several forms, but all forms of phishing are methods of exploiting human behavior in order to gain access to sensitive, valuable information. Phishing attacks may come through emails, social media accounts, workplace programs and other systems that are prone to human access and error.
After the global events and digital transformation of the world in 2020, phishing attacks increased. They were found in 36% of breaches in 2021, up from 25% in 2020. The end goal in many phishing scams is to get hold of a victim’s credentials to gain access to their accounts, which might include everything from personal financial information to confidential work data.
Types of Phishing Attacks
Phishing attacks will vary in who they target and how they operate. Some common methods of collecting data are to outright request information from the victim or to insert malicious links into legitimate-looking emails that place malware on the victim’s device to collect the desired data. These links could also insert ransomware that encrypts data and holds it hostage until the victim provides the information the hackers want.
The different types of phishing attacks include:
- General phishing: These attacks may be sent out broadly and indiscriminately. They’re not targeting anyone in particular — just anyone who’s willing to take the bait. Often, they’ll attempt to make emails that look like they’re from commonly used websites and send them to everyone, whether the targets use the site or not, to get someone to bite. It’s not going to be the route with the most clicks, but it casts a broad net.
- Spear phishing and whaling: Spear phishing focuses on a specific person or organization. It involves research on the target, such as through social media or company websites, before sending personalized emails designed for them. Whaling is another type of spear phishing that focuses specifically on senior management. These attacks are often more sophisticated and disguised in corporate language. They may even attempt to impersonate the “whale” and use its authority to convince other employees to reveal sensitive information or complete certain tasks.
- Vishing: Vishing is done over the phone. These calls might be a recording or a real person and generally include vague threats and a false sense of urgency to convince the person to disclose sensitive information. As with emails, they may attempt to impersonate other organizations, such as the Internal Revenue Service (IRS), a bank or law enforcement agencies. The caller typically spoofs their ID so the call appears to come from a trusted source or a local area code.
- Smishing: Similar to traditional phishing, smishing occurs over text messages. These attacks also call for immediate action and might be vague, prompting the victim to click a malicious link to get more information.
- Clone phishing: A clone phishing attack directly copies a legitimate email from an organization and replaces links with ones that redirect to a malicious website. They might impart malware or trick the user into thinking they’re entering their login credentials into the legitimate company’s website. In fact, they’re sending them over to the hackers.
CHARACTERISTICS OF A PHISHING EMAIL
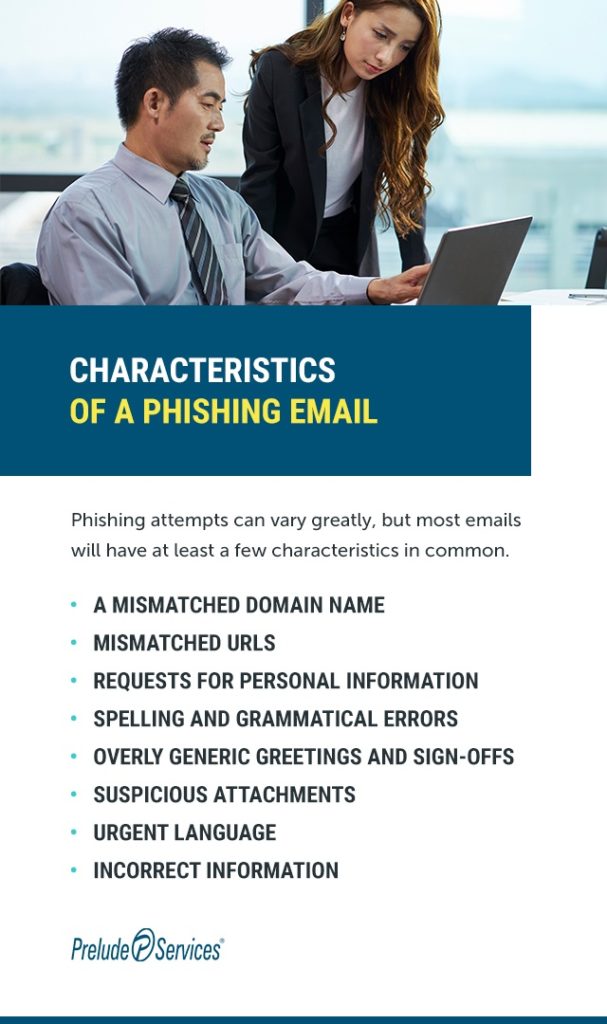
Phishing attempts can vary greatly, but most emails will have at least a few characteristics in common. Always be on the lookout for the following hints:
- A mismatched domain name: If an email says it’s from “Prelude Services” but the sender is “prs728@gmail.com,” you’re not looking at a legitimate email. Business emails will generally come from private domains — in our example, preludeservices.com — and will have professional phrases before the @ symbol, such as “information” or “sales.” Be sure to click on the name of the sender if you can’t see this right away. Some email clients will show a display name instead of the full email address.
- Mismatched URLs: A link may look like it leads to one place and then take you somewhere entirely different. Look out for these URLs by hovering over them. The real link should appear, either by your mouse or on the bottom left-hand corner of your email client. Be especially wary of links that are shortened, such as through a “bit.ly” URL or those that look very similar to the real thing. Hackers might swap two letters or use similar-looking combinations to trick you, such as “rn” instead of the letter “m” in a URL.
- Requests for personal information: Most legitimate companies are not going to ask you to share your personal data. This kind of request almost always signifies a phishing attempt. Internal business information should also never be shared over email. If someone in your company requests it, follow proper policy to get the right information to the right people without complying with a phishing request.
- Spelling and grammatical errors: These errors quick way to spot phishing emails. They’re often rife with spelling errors and grammar mistakes that native speakers wouldn’t make. Real emails from reputable companies generally go through a strict editing process that will catch typos.
- Overly generic greetings and sign-offs: When you’re already signed up with a company, they typically have your name on file. So, you can expect an email to say something like, “Hey [Name].” If you get an email that starts with something like “Hello customer,” that’s usually a hint that it is not legitimate. You can also expect illegitimate emails to have generic sign-offs. Instead of the name and title of an employee, the email might be from a generic customer service agent.
- Suspicious attachments: Many times, phishing scams attempt to plant malware on the user’s computer. If your computer asks you to change your security settings or grant permission, do not open the attachment. Be especially wary of .zip files.
- Urgent language: Phishing scams will typically try to make their victims feel like they have to take action right away or risk significant consequences. They want you to act quickly and not think things through. These scare tactics are typically used by hackers, who sometimes ramp up their efforts in times of stress.
- Incorrect information: If you look up the company’s information and spot inconsistencies, such as the wrong location for their headquarters, that’s another clue that you’re looking at a fake.
How to Prevent Attacks
Fortunately, there are many steps you can take to prevent phishing attacks. Implement the following practices to keep phishing attacks to a minimum and put a stop to them when they come through.
1. STAY VIGILANT
Be aware of the characteristics listed above and make sure you’re able to spot a phishing email. You must carefully inspect every email that comes your way and get in the habit of checking URLs and attachments for integrity before clicking on them. If you’re in charge of a team, make sure they are well-informed on what to look for in a phishing email, too.
If you’re ever unsure of an email, there are easy ways to confirm its authenticity. Access the official website of the organization or find their phone number through trusted channels, such as a saved bookmark on your web browser — not the information provided in the email. If you know the person who sent an email, such as someone in your company, you could give them a call, too.
2. KEEP SOFTWARE UPDATED
Although software updates can seem like a nuisance in the moment, they’re essential for keeping your cybersecurity methods up to date. These updates often include patches that were specifically designed to address vulnerabilities that may have appeared in your software. One of the largest cyberattacks in history occurred in 2017 because Equifax, a massive credit reporting agency, failed to fix a well-known vulnerability in its software. That vulnerability was addressed in a patch, but lax security processes meant that they did not install it, leaving them open to hackers.
Include software updates in your regular maintenance practice or set up automatic updates to ensure your security software stays functional. Phishing methods can evolve quickly, so you need to make sure your software offers up-to-date protection.
3. USE PASSWORD BEST PRACTICES
Credentials are the most sought-after type of data involved in breaches and are present in about 60% of them. Users can take a few different approaches to their credentials and follow best practices for passwords:
- Don’t repeat passwords.
- Make long passwords with varied capitalization, special characters and numbers, and do not include information that’s easy to find about you, such as a birthday or child’s name.
- Start using a trusted password manager.
- Use multi-factor authentication (MFA), which adds extra protection by confirming your access from another app or device.
Businesses can help their employees by enabling MFA on all work programs.
4. INSTALL SECURITY SOFTWARE
Security software is another excellent way to prevent the worst effects of phishing scams. These programs can offer various support structures, such as:
- Email screening: Security programs integrated with your email client can do everything from scanning emails for potential phishing characteristics to evaluating attachments for viruses and hidden files. These services can keep phishing attacks out of the picture entirely by sending them straight to spam with little room for human error.
- Web browser security: Web browser security can offer alerts upon visiting a risky link and block potentially dangerous downloads. Even if a user clicks a suspicious link, these programs can help keep the user from submitting their information or downloading potential malware.
- Firewalls: Firewalls block malicious packets of data that cross a network, preventing users from downloading viruses and malware.
5. CLEAN UP YOUR ONLINE PERSONA
Make sure that you don’t have a wealth of information about yourself posted online. Hackers shouldn’t be able to retrieve personal details about you that they could then use to impersonate or deceive you in a phishing attack. Do a sweep of all social media profiles and evaluate the information you have available, removing it if necessary.
6. BACK UP YOUR DATA
One method of phishing is to install ransomware that keeps your data encrypted until you provide the requested information. To ensure that these attempts don’t hold your important data hostage, you can keep your data copied onto a safe, secondary location such as a cloud service or an external hard drive. This consideration is especially important for businesses, which might face significant interruptions if hacked.
What to Do if You or Your Employee Responds to a Phishing Email
If a member of a business has responded to a phishing email, you’ll need to take appropriate action related to the kind of attack. If they clicked on an unsafe link or accidentally downloaded malware, update their security software and scan the system. Ideally, this process will catch the malware, but backing up your data is also a good idea. If a user has accidentally submitted their credentials to a scammer, they should immediately reset their password and check for any suspicious activity.
Individuals who gave out their personal information should visit IdentityTheft.gov and follow the listed steps.
What to Do if You Suspect a Phishing Attack
When a phishing email does make its way to your inbox, you should know where to send it to shut down the operation.
Businesses should have a process in place to investigate phishing emails so workers can forward any suspicious messages to the IT department. One common practice is to send out fake phishing emails to detect the employees’ abilities to catch them and their overall compliance with the forwarding program.
While individuals don’t have their own personal IT departments, they can still send any phishing emails to a higher authority. In these instances, and for businesses that don’t intend to start a phishing prevention program, users can forward emails to the Anti-Phishing Working Group (APWG), an international coalition dedicated to the fight against cybercrime, or to the Federal Trade Commission (FTC).
Contact Prelude Services for IT Services to Protect Against Phishing Attacks
Phishing attacks can be sophisticated, and preventing them requires a multifaceted approach. If you’re in the business of healthcare, the experts at Prelude Services can help you find and implement the right phishing prevention plan for your needs. We have a skilled team dedicated to IT with specific considerations for healthcare organizations.
Keeping your patients’ data safe to the best of your ability is key to staying compliant with industry regulations, and phishing poses a threat to that data. Reach out to us today to learn more about how we can protect your business and your patients with phishing prevention strategies.

CONTACT PRELUDE SERVICES FOR 24/7 IT SUPPORT
Technology has become a crucial part of the modern business experience. Without functional computers and mobile phones, many business practices would grind to a halt. Unfortunately, breakdowns and malfunctions are an inevitable part of any machine, meaning businesses do grind to a halt until the issues are fixed. In order to keep your business running, it's crucial to have access to IT support when you experience technical difficulties.
If you're a healthcare company, long-term care provider, or small business in need of IT support at all hours, consider Prelude Services. We're a SSAE SOC
Compliant business dedicated to improving your security and functionality. We offer specific IT services for senior living care, nursing homes, retirement home services and assisted living, including 24/7 IT support. If you want to know how Prelude can help you, contact us today!
